
If the internet had a list of most important protocols, TCP/IP would get top billing. HTTPS would be right behind it. Somewhere a few lines down, in tiny print, would be BGP. Which is strange, because without BGP the internet simply wouldn’t work. Every time you visit a website, BGP is quietly deciding which path your packets should take across the globe. It’s the protocol that holds the whole thing together, and almost nobody outside networking has ever heard of it. When it goes wrong, half of Facebook goes dark and network engineers stop sleeping for a week. When it goes right, which is almost always, it disappears into the background like plumbing.
The Internet Isn’t One Network
First, throw away the idea of “the internet” as a single network. The internet is actually about 75,000 smaller networks that agreed to talk to each other. Each one is called an Autonomous System, or AS. Your home ISP is an AS. Google is an AS. Amazon, Netflix, your university, and Cloudflare are each an AS. Every AS has a number, like AS 15169 for Google or AS 32934 for Meta, that’s used in routing conversations.
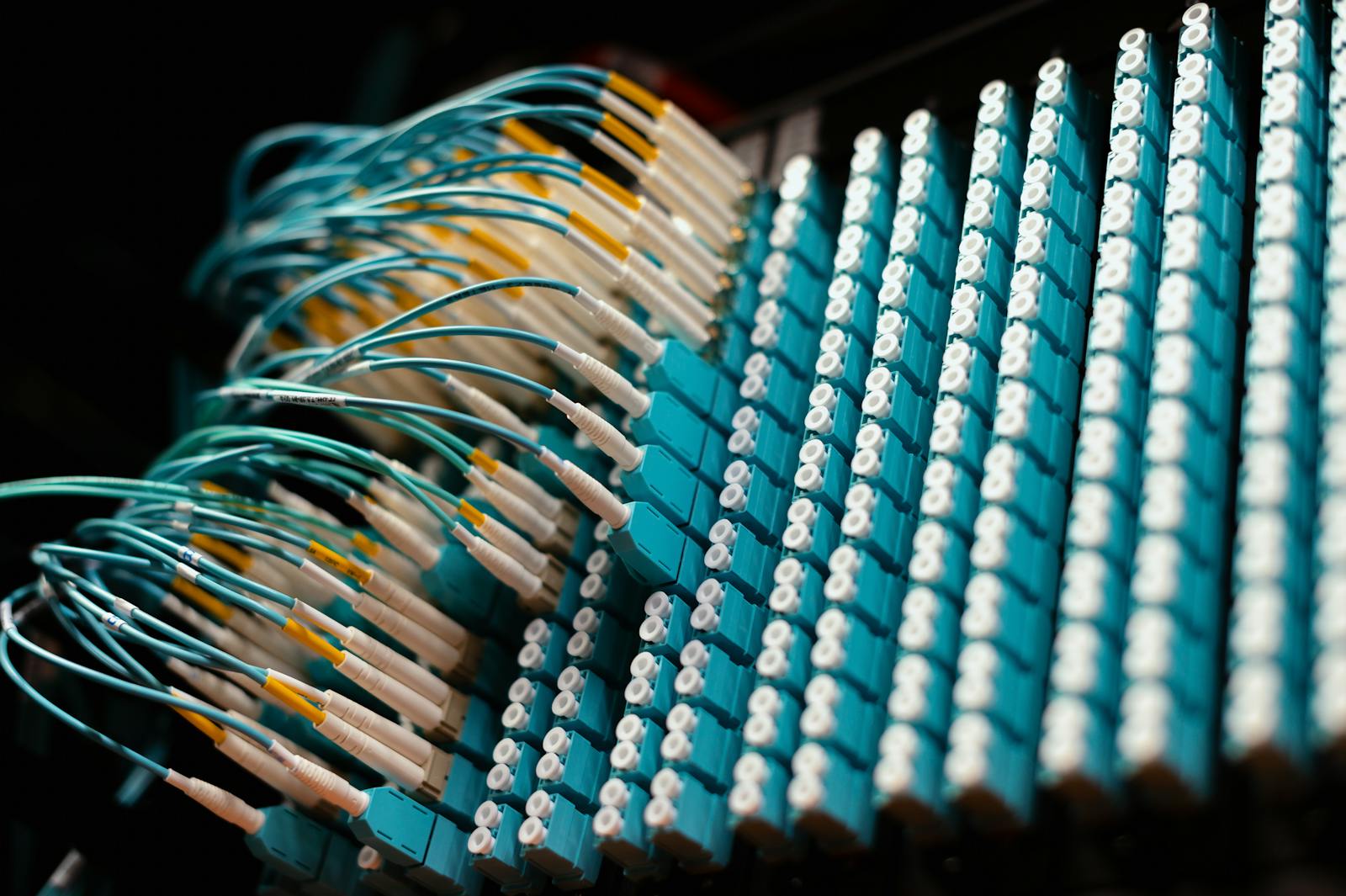
These networks connect to each other in messy, overlapping ways. Some pairs of networks peer directly, trading traffic for free because they both benefit. Others pay for transit, routing their traffic through bigger networks to reach the wider internet. Big content providers connect at internet exchange points, which are physical buildings full of cables where dozens of networks meet. The actual topology looks less like a neat tree and more like a tangled nest of relationships that’s been growing organically for decades.
So when your phone asks a website in Tokyo for a cat video, the traffic has to hop across several Autonomous Systems to get there. Your ISP hands the packets off to a regional carrier. The regional carrier hands them off to a global backbone. The backbone hands them to an Asian carrier. The Asian carrier hands them to a Japanese ISP. The Japanese ISP hands them to the server. Each handoff happens at the border between two Autonomous Systems. But how does each network know which direction to send the traffic? That’s BGP’s job.
What BGP Does
BGP stands for Border Gateway Protocol. Its job is simple to state and fiendishly hard to implement: networks tell each other, “If you want to reach this range of IP addresses, send the traffic to me, and I’ll get it there.” Each network collects these announcements from its neighbors, picks the best route for each destination based on rules it has configured, and then passes the announcements along with itself added to the path.
The result is a constantly updating global map of who can reach whom and by which route. There is no central authority deciding these routes. There’s no master database someone queries. The whole thing emerges from networks gossiping with each other, moment by moment, in near real time. Each network maintains its own copy of the map, and they mostly agree, and when they disagree, they update each other until they agree again.
That map has to converge fast enough that a cat video from Tokyo actually reaches your phone in Jamnagar within a second, even as cables break, ISPs fail, business relationships change, and new networks come online every day. When BGP is working well, it’s one of the most impressive distributed systems humanity has ever built. When it’s working badly, it’s a global crisis.
Why It Quietly Terrifies Network Engineers
BGP runs almost entirely on trust. When a network announces, “I can reach these IP addresses,” neighboring networks generally just believe it. If someone announces routes they shouldn’t, intentionally or accidentally, traffic for entire countries can suddenly start flowing through the wrong place. This has happened many times, and every time it’s a headline.
In 2008, a Pakistani ISP tried to block YouTube inside Pakistan by announcing a false route to YouTube’s IP range. The announcement leaked outside Pakistan, and YouTube went offline for much of the world for several hours while network engineers scrambled to fix it. In 2017, a small ISP in Russia briefly hijacked traffic destined for major financial companies, meaning visitors to their websites had their traffic routed through Russian networks before reaching the real servers. Nobody knows for certain what was done with that traffic. In 2021, a BGP misconfiguration knocked Facebook, Instagram, and WhatsApp offline for six hours, affecting about three billion users and costing Facebook an estimated $100 million. A few lines of BGP config touched the wrong way will embarrass a Fortune 500 company. A few lines touched maliciously can reroute bank traffic through a country that wants to read it.
BGP assumes everyone is honest. When a single network announces it owns IP space it does not own, by mistake or on purpose, the rest of the internet often just believes it. That is a "BGP hijack."
Route Leaks and Hijacks
There are two main ways BGP goes wrong. The first is a “route leak,” which is usually accidental. A network is supposed to tell its neighbors only about routes it handles itself, but due to a misconfiguration it accidentally announces routes it heard from other neighbors. Traffic that was supposed to go one way suddenly gets redirected through the leaking network, which often can’t handle the load, and things slow down or fall apart.
The second is a “BGP hijack,” which can be either accidental or deliberate. A network announces routes it doesn’t own, claiming to be the right destination for some range of IP addresses. If enough neighbors believe it, traffic flows through the hijacker instead of the real owner. Hijacks have been used to steal cryptocurrency by rerouting traffic to fake wallet services, to eavesdrop on sensitive communications, and occasionally just to prove a point about how fragile the system is.
How They’re Trying to Fix It
The industry has been slowly rolling out security extensions to BGP. The most important is RPKI, which stands for Resource Public Key Infrastructure. It lets networks cryptographically prove that they’re authorized to announce specific IP address ranges. Neighboring networks can then verify the signature and reject announcements that don’t check out. Adoption has been steady. Most major cloud providers now use it, as do many large ISPs. But BGP itself is still trusting at its core. There’s no global rollout of a more secure replacement, because replacing the protocol that runs the internet while the internet is running is not a weekend project.
Network engineers also use route monitoring services that watch the global BGP table and send alerts when something looks suspicious, like when a small ISP in a country you don’t operate in suddenly announces a route to your company’s IP space. It’s not a fix, but it’s at least a smoke detector. The major cloud providers have entire teams whose job is to watch BGP for signs of trouble and respond within minutes when something looks off.
BGP misconfigurations have taken Facebook offline for hours, sent Russian traffic through Chinese networks, and once accidentally null-routed YouTube globally. None of those required a hack, only a typo.
Why You Should Care
Most people will never read a BGP announcement in their lives, and that’s fine. But understanding that the internet runs on mutual trust between thousands of networks explains a lot of what you see in the news. When a whole region loses the internet, it’s usually BGP. When one company’s outage takes down five unrelated websites, it’s usually BGP. When a government “switches off” the internet in a country, they’re usually ordering local networks to stop announcing BGP routes for that country’s IP space.
BGP is also why the internet is so hard to destroy and so easy to disrupt. No single authority can shut it down because no single authority runs it. But a single misconfigured router can ruin a Monday for millions of people. The same decentralization that makes the internet resilient also makes it fragile in specific, surprising ways.
A Short History of How BGP Got Here
BGP was designed in 1989 by two engineers, Kirk Lougheed and Yakov Rekhter, during a conference lunch. The story goes that they sketched the original design on three napkins, which is why BGP is sometimes called the “three-napkin protocol.” It was intended as a quick fix for a growing problem: the old routing system, called EGP, couldn’t scale to the number of networks that were joining the early internet.
That “quick fix” has now been running the entire internet for over thirty years. Various successor protocols have been proposed, debated, and partially deployed. None have replaced BGP. The reason is the same reason we still drive on roads designed for horse-drawn carriages: the cost of switching everything simultaneously is prohibitive, and the pieces of the system that work are good enough to keep. BGP gets patched and extended, but its core remains the same routing protocol sketched on napkins in 1989.
Who Actually Runs BGP
Every Autonomous System has BGP running on its border routers, the machines that physically connect to neighboring networks. These routers are usually specialized hardware from companies like Cisco, Juniper, or Arista, running software written specifically for handling the global routing table. The global routing table currently has over 950,000 entries, and it keeps growing as more networks and IP address blocks come online.
The people who configure these routers are network engineers, and the field is small enough that the senior practitioners tend to know each other by name. When something goes catastrophically wrong, there are Slack channels and mailing lists where engineers from different companies can coordinate a response in real time. It’s a remarkably informal system for something that runs the internet, and that informality is both its strength and its weakness. When someone makes a mistake, the community tends to figure it out quickly. When someone acts in bad faith, the same trust that makes the community work can be exploited.
My Honest Take
BGP is ancient by internet standards, weirdly fragile, and absolutely essential. It’s the internet’s accidental operating system, designed in the late 1980s as a temporary fix and still running everything thirty-plus years later. When it works, it’s invisible. When it breaks, half of your favorite apps go offline at the same time. That’s BGP: the most important protocol you’ve never heard of, held together by convention, shared interest, and the reluctant cooperation of 75,000 networks who agreed, a long time ago, to tell each other the truth about where to send the traffic.
Key Takeaways
- BGP is the routing layer of the entire public internet, and it is built on trust, not cryptography.
- Most major outages and "the internet broke" incidents trace back to BGP misconfigurations or hijacks.
- RPKI and route-origin validation are the industry’s slow, multi-year attempt to bolt verification onto a protocol that never had it.
Start Your Free Trial Today
Full All-Access to hands-on labs, PBQs, and certification tracks, no credit card required.
Start Free Trial